The Quantum Computing Arms Race: Technology, Security, and Global Power
As the U.S. and China compete for quantum supremacy, the technology threatens to render current encryption obsolete while promising transformative breakthroughs in science and medicine
September 26, 2024
Executive Summary
Quantum computers represent one of the most consequential technological frontiers of the 21st century, promising exponential advances in molecular simulation, drug discovery, materials science, and fundamental physics. Major research institutions, including IBM, are racing toward practical quantum systems capable of solving previously intractable problems within minutes rather than years.
Yet beneath the scientific optimism lies a critical security vulnerability: quantum computers will possess the ability to decrypt virtually all current internet encryption within minutes, compromising everything from state secrets to financial transactions stored today. Intelligence agencies and technology leaders now warn of a “store now, decrypt later” threat—the possibility that adversaries are already harvesting encrypted data to crack once sufficiently powerful quantum machines arrive.
The United States maintains current leadership in quantum development, but China has mobilized significant state resources, investing over $15 billion and holding more than half of all quantum patents globally. The race is reshaping geopolitical competition, national security strategy, and global macro investment frameworks, with profound implications for the future of digital security and technological dominance.
Key Takeaways
- Quantum computers harness superposition and entanglement to perform simultaneous calculations on exponential scales, potentially completing computations in minutes that would take classical supercomputers millions of years.
- IBM, Google, and others are targeting practical quantum systems by the early 2030s, representing a fundamental shift in computing paradigm and scientific capability.
- Quantum computers can crack current RSA encryption—the standard securing everything from banking to classified communications—within hours or minutes rather than the centuries required by classical systems.
- China has invested over $15 billion in quantum research, more than triple any other nation, and holds majority share of quantum-related patents, signaling a comprehensive national strategy.
- The U.S. government has responded with the Chips and Science Act and restricted technology exports to China, elevating quantum to the status of critical national security technology.
- Quantum key distribution and other quantum-secure protocols are already in early deployment by financial institutions and governments to mitigate future decryption risk.
- Unlike previous technological races, quantum advancement benefits all nations through scientific discovery, but asymmetric cryptographic advantages create powerful incentives for dominance.
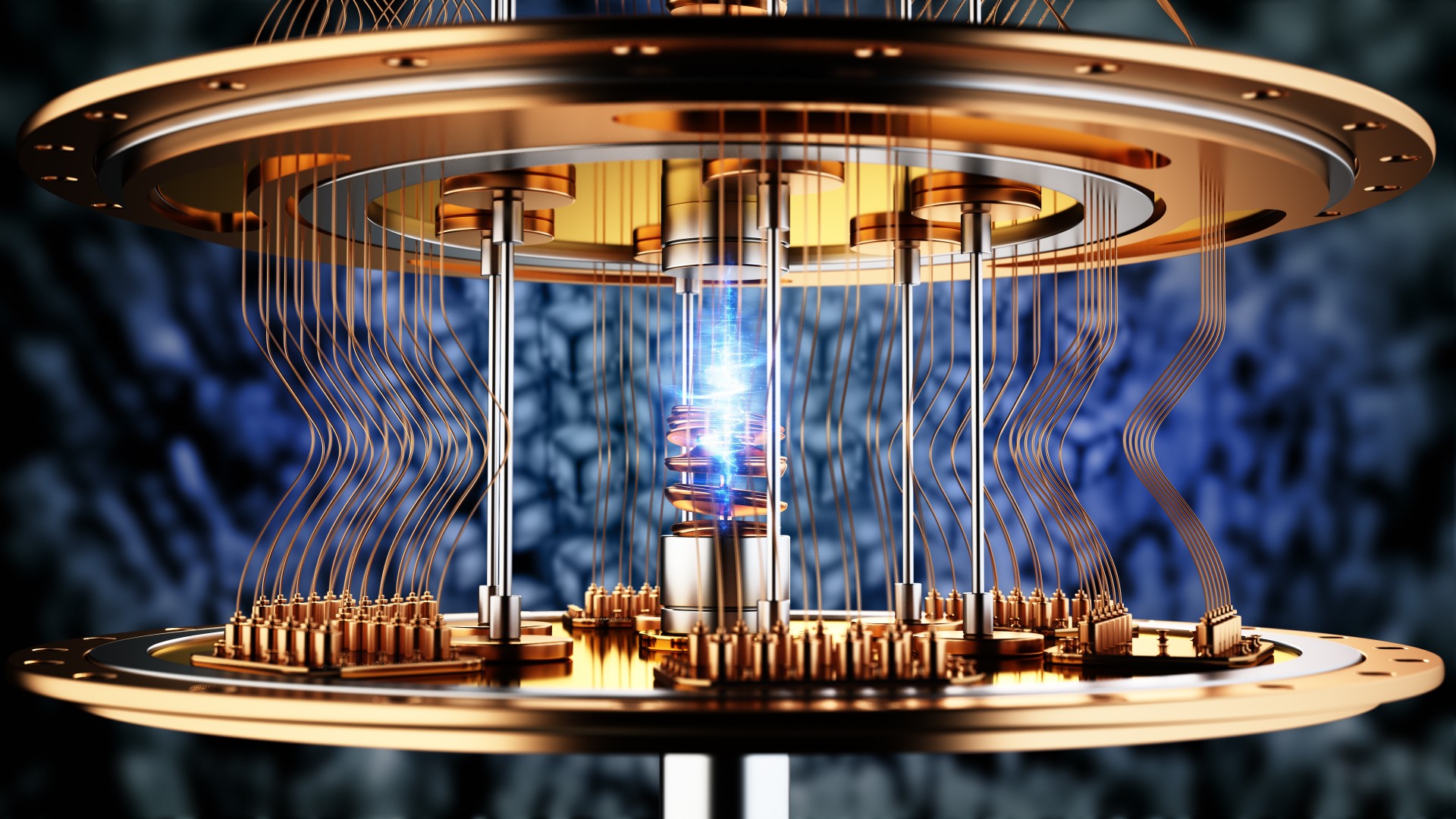
The Quantum Frontier: A Visual Primer
Bloomberg Originals produced an in-depth documentary on the quantum computing race, exploring both the scientific breakthroughs and the geopolitical stakes:
Event Overview: The Quantum Milestone
IBM’s Quantum System Two, housed at the company’s research facility in upstate New York, represents a milestone in practical quantum computing. The machine integrates 133 qubits—quantum bits capable of existing in superposition—on a single Heron chip, advancing the field toward systems capable of useful computation beyond theoretical demonstration.
The system requires extreme cooling—chilling the quantum processor to temperatures colder than the cosmic microwave background—to preserve the delicate quantum states that define the machine’s computational advantage. This engineering challenge underscores why quantum computing remains decades away from ubiquitous deployment despite decades of fundamental research.
IBM has publicly committed to achieving practical quantum advantage by 2033, with the company spending several billion dollars annually across its quantum program as part of a seven-billion-dollar annual research and development budget. Yet IBM acknowledges that quantum leadership requires sustained, global-scale investment—a threshold few organizations can meet.
Background: From Theory to National Strategy
Quantum mechanics—the physics governing subatomic particles—has been understood since the early 20th century, yet harnessing it for computation remained theoretical until recent decades. The key insight is that quantum bits, unlike classical binary bits, can exist in “superposition,” simultaneously representing both 0 and 1 until measured.
This property enables quantum computers to explore multiple solution paths in parallel. Where a classical computer solving a maze must test each path sequentially, a quantum computer can evaluate all paths simultaneously, arriving at the solution exponentially faster for certain problem classes. The catch: quantum states are extraordinarily fragile, collapsing when disturbed by heat, electromagnetic radiation, or other environmental noise.
Decades of incremental progress have yielded systems with increasing qubit counts, but “quantum error correction”—the ability to maintain accurate computation amid inevitable noise—remains unsolved at commercially relevant scales. Most experts estimate practical quantum computers capable of economically useful computation remain 5-10 years away, though timelines remain highly uncertain.
Recognition of quantum computing’s potential has elevated it to national strategic priority. The United States, China, the European Union, and others have initiated multibillion-dollar quantum research programs, integrating quantum development into broader technology and defense strategies.
Why Quantum Computing Matters: Scientific and Economic Implications
Quantum computers promise transformative advances in three domains: scientific discovery, economic innovation, and—critically—national security.
On the scientific front, quantum machines will enable molecular-level simulation impossible with classical computers. Drug designers could model protein interactions at atomic precision, dramatically accelerating discovery of treatments for cancer, neurological diseases, and other intractable conditions. Materials scientists could optimize battery chemistry, superconductors, and industrial catalysts with unprecedented accuracy. Fundamental physicists could simulate quantum systems directly rather than through approximation, potentially unlocking new physics.
Economically, the first nations and organizations to harness practical quantum computing will acquire substantial competitive advantage across pharmaceuticals, materials, finance, and optimization. Quantum-accelerated machine learning could enhance artificial intelligence capabilities. Quantum cryptanalysis threatens current cybersecurity models, creating demand for quantum-resistant encryption—an entirely new market.
Yet the most immediate strategic concern is cryptographic: quantum computers will render obsolete the RSA encryption securing roughly 90% of internet communication. A single sufficiently powerful quantum computer could crack in minutes the cryptographic keys that would require a classical computer trillions of years to break. This threshold—what researchers call “cryptographically relevant quantum computers”—could arrive within a decade according to conservative estimates.
The Encryption Crisis and National Security
The prospect of quantum-enabled decryption has triggered urgent action across financial institutions, governments, and intelligence agencies. HSBC, one of the world’s largest banks, processes 3.5 trillion pounds in annual payments and faces existential risk if quantum-enabled attacks compromise customer account security and trust.
The banking sector now contemplates what specialists term “harvest now, decrypt later” attacks—the scenario in which adversarial state actors or criminal organizations are actively intercepting and storing encrypted communications today, with the intent to decrypt them once quantum computers mature. This threat is not hypothetical; U.S. intelligence agencies have publicly warned that such collection campaigns are likely underway.
State secrets, military communications, diplomatic cables, and intelligence identities encrypted today could be exposed tomorrow. The implications extend to espionage, counterintelligence, and national military advantage. A nation that achieves quantum cryptanalysis capability first gains an asymmetric intelligence advantage that could persist for years.
This reality has prompted wealth preservation and security-focused institutions to accelerate adoption of quantum-resistant cryptography. HSBC and others are testing quantum key distribution—a protocol using single photons to generate encryption keys that fundamentally cannot be intercepted without immediate detection, thanks to quantum mechanics’ enforcement of the observer effect.
The U.S.-China Quantum Competition
China views quantum computing as a strategic national asset, not merely a technological frontier. The country has mobilized state resources at scale, establishing dozens of dedicated research institutes and committing over $15 billion to quantum development—more than three times the investment of any other nation.
Chinese researchers hold more than 50% of all quantum-related patents filed globally, according to security analysts advising the U.S. government. This dominance in patent creation reflects both China’s substantial research workforce and its systematic approach to intellectual property accumulation as a strategic instrument.
In 2016, China achieved a headline breakthrough by launching Micius, a quantum communications satellite capable of sending quantum-secured keys over far greater distances than ground-based fiber optic networks. China subsequently built a domestic quantum network connecting banks, government agencies, and research institutions—infrastructure the United States lacks.
The United States has responded through export controls targeting advanced semiconductors and fabrication tools critical to quantum research, restrictions on technology transfer to Chinese institutions, and acceleration of the Chips and Science Act—a multibillion-dollar initiative to bolster domestic research and manufacturing capacity.
Yet American researchers face a structural disadvantage: the equivalent quantum labs in China employ 50-100 graduate students and postdoctoral researchers, while comparable U.S. programs operate with 4-6 researchers. Funding disparities compound the scale imbalance, requiring U.S. institutions to offset Chinese resource advantages through innovation and scientific agility.
Quantum Key Distribution: The Emerging Defense
While quantum computers threaten traditional encryption, quantum physics simultaneously offers a solution: quantum key distribution. This approach leverages the fundamental quantum mechanical principle that observing a quantum system alters its state—making eavesdropping immediately detectable.
Quantum key distribution systems encode cryptographic keys into single photons transmitted through fiber optic cables. If an eavesdropper attempts to intercept and measure the photons, the quantum state collapses, rendering the key useless and triggering an alert. The sender and recipient know instantly that communication has been compromised.
BT Group, the British telecommunications company, has deployed quantum key distribution between London and Berkshire using existing fiber infrastructure, securing financial data transmissions for HSBC. Singapore’s National University has launched quantum satellites designed to distribute quantum-secured keys globally using optical telescopes and smaller, more cost-effective spacecraft than China’s Micius satellite.
Deployment of quantum-secure infrastructure faces logistical challenges: fiber optic cables have distance limitations (typically 100-200 kilometers before signal degradation), necessitating satellite networks or relay stations for global coverage. But the security guarantees are unmatched—no quantum computer, regardless of computational power, can crack a quantum-distributed key.
The Collaboration Paradox: Scientific Progress vs. Security Restrictions
Quantum research developed in an era of greater international openness—the late 1980s and 1990s when geopolitical tensions were lower. Scientists from the U.S., China, Europe, and elsewhere exchanged ideas freely, collaborated on shared problems, and viewed quantum science as a collective human endeavor.
That collaborative spirit persists among many researchers but conflicts increasingly with national security imperatives. The U.S. has restricted collaboration with Chinese quantum institutes and companies, limiting technology transfer and joint research. IBM, Google, and Microsoft no longer partner with Chinese organizations on quantum development, acknowledging quantum as a “sensitive technology” with “big national security implications.”
Yet premature imposition of export controls and collaboration restrictions risks delaying quantum breakthroughs across all nations. Scientists and policymakers face a tension: early security-driven restrictions slow innovation; late controls fail to protect classified knowledge already disseminated. The optimal timing of security lockdown remains contested.
International researchers in neutral jurisdictions—notably Singapore’s Centre for Quantum Technologies—continue collaborating with both U.S. and Chinese partners while navigating geopolitical constraints. This middle ground may prove crucial for maintaining scientific progress while managing security risks, though political pressure to restrict collaboration continues rising.
Quantum Computing: Strategic Snapshot
| Factor | Current Status | Strategic Implication |
|---|---|---|
| Quantum Computer Maturity | Experimental systems (100-300 qubits); practical applications 5-10 years away | Narrow window to deploy quantum-resistant encryption before cryptographic threat materializes |
| U.S. Investment | Multiple billions annually across IBM, Google, universities, government | Maintains technical leadership but lags China in aggregate resource commitment |
| China Investment | $15+ billion cumulative; 50%+ of quantum patents; Micius quantum satellite operational | Rapid capability expansion; potential for cryptanalysis dominance if first to scale |
| Encryption Vulnerability | RSA and similar encryption vulnerable to quantum attack; “harvest now, decrypt later” campaigns likely underway | Existential risk to financial systems, state secrets, military communications if quantum computers arrive before migration to quantum-resistant methods |
| Quantum Key Distribution | Early deployment by HSBC, BT, government agencies; satellites in development | Technologically proven but infrastructure-intensive; gradual adoption expected |
| Technology Export Controls | U.S. restricts semiconductor access to China; limits collaboration with Chinese labs | Slows Chinese progress but risks retaliation and reduces scientific collaboration benefits |
Risk Factors and Critical Watchpoints
- Cryptographic Transition Timeline Risk: If practical quantum computers arrive before quantum-resistant encryption is universally deployed, a brief window exists for mass decryption attacks. Current migration timelines may be insufficient.
- State-Sponsored “Harvest Now, Decrypt Later” Campaigns: Intelligence agencies likely already collecting encrypted data today for future decryption. Classified communications, diplomatic cables, and military systems encrypted today could be compromised within years.
- Chinese Cryptanalysis Advantage: If China achieves cryptographically relevant quantum computers before the U.S., Beijing gains asymmetric intelligence advantage over decades. Military, economic, and diplomatic implications would be severe.
- Financial System Vulnerability: Banking and payment systems rely on encryption for account security, fund transfers, and customer trust. Quantum-enabled breaches could trigger systemic financial instability.
- Supply Chain and Intellectual Property Espionage: Quantum computers could retroactively decrypt stolen intellectual property, trade secrets, and research data held by competitors or adversaries. Strategic technology companies face elevated historical exposure.
- Overregulation of Quantum Research: Premature security lockdown of international collaboration may slow quantum breakthroughs, leaving all nations worse off. The optimal security-innovation balance remains unresolved.
- Quantum Technology Singularities: If quantum computing breakthroughs arrive suddenly rather than incrementally, currently unknown vulnerabilities may emerge. Tail risks of catastrophic systems failures remain difficult to quantify.
What Comes Next: Timeline and Trajectories
The quantum landscape will evolve across multiple concurrent timeframes. Near-term (2025-2028), governments and financial institutions will accelerate quantum-resistant encryption migration. NIST has already published standards for post-quantum cryptography, enabling organizations to begin legacy system upgrades.
Investment in quantum key distribution infrastructure will likely intensify, particularly among nations facing highest espionage risk: financial centers, defense contractors, intelligence agencies, and governments with high-value secrets. Satellites for global quantum communications will likely proliferate, with China advancing Micius-class systems and the U.S. developing comparable or superior alternatives.
Mid-term (2028-2033), quantum computers may achieve practical advantage in narrow application domains—drug discovery, materials optimization, certain machine learning tasks. This milestone will validate decades of research and likely trigger substantial capital reallocation toward quantum-enabled applications.
The geopolitical dimension will simultaneously intensify. Technology export controls will likely tighten, particularly around semiconductors and computing equipment critical to quantum research. International collaboration will fragment further unless deliberate diplomatic efforts preserve shared scientific progress.
Long-term (2033+), the quantum computing landscape could resemble artificial intelligence today: transformative across multiple domains, concentrated among well-resourced organizations, and subject to ongoing national security concerns. The first organization or nation achieving cryptographically relevant quantum computers will possess extraordinary asymmetric advantage for years before competitors catch up.
Conclusion
The quantum computing race represents one of the defining technological and geopolitical competitions of the 21st century, combining promises of scientific breakthrough with urgent security imperatives. Unlike previous technological races—space exploration or nuclear weapons—quantum advancement benefits all humanity through scientific progress, yet asymmetric capability creates powerful incentives for dominance.
The United States currently leads in quantum computing development, but China’s systematic resource mobilization and intellectual property accumulation signal rapid advancement toward parity or potential dominance. The stakes extend beyond commercial advantage to encompass national security, military capability, intelligence operations, and financial system stability. A nation that achieves cryptographically relevant quantum computers first gains an intelligence advantage potentially measured in decades.
The encryption crisis—the imperative to deploy quantum-resistant cryptography before quantum computers mature—demands urgent action. Banks, governments, and technology companies face a narrow window to migrate legacy systems before the threat materializes. The work of researchers like those at IBM, China’s institutes, and Singapore’s Centre for Quantum Technologies represents humanity’s effort to navigate this transition safely.
For investors, policymakers, and strategic communicators monitoring this landscape, the dominant themes are acceleration, stakes elevation, and uncertainty. Watch for breakthroughs in quantum error correction, announcements of expanded quantum computing systems, progress on quantum-resistant encryption migration, and shifts in international collaboration or export controls. The quantum future is not yet determined—but the race to shape it has already begun.
TrustScoreFX Editorial — Independent analysis of technology, geopolitics, and macroeconomic developments.
This article is for informational purposes and does not constitute investment or security advice. Readers should consult qualified professionals for decisions involving technology, cryptography, or national security policy.
© 2024 TrustScoreFX. All rights reserved.